Overview:
WPA3 has brought in new advantages over WPA2 in order to overcome issues such as Offline Dictionary Attacks and provide advantages of forward Secrecy. This does look promising to secure existing WPA2 networks that are currently in use. In general, WPA3 doesn’t define new protocols but instead raises mandatory support for existing protocols that already exist. The only new feature that was added in WPA3 is the transition mode wherein the devices that support only WPA2 can as well connect to a WPA3 Authentication based SSID. This makes WPA3 backward compatible with WPA2. The WPA3 certificate mandates the support for SAE (Simultaneous Authentication of Equals) handshake. There were several other variants of SAE introduced during earlier research however this one (the one mentioned in WPA3 certification) was commonly referred to as DragonFly.
ECC (Elliptic Curve Cryptography):
The SAE handshake supports both Finite Field Cryptography (FFC) using multiplicative groups modulo a prime (MODP groups), and it supports Elliptic Curve Cryptography (ECC) using Elliptic curve groups modulo a prime (ECP groups). The WPA3 standard mandates the use of ECC for all Encryptions and all others are optional. So I would like to discuss more on ECC than others because not only this is used in WPA3 but many other Encryption requirements have started using the same technology for better encryption. The reason to use this new cryptography technique is the need for a better trapdoor function. The existing RSA and Diffie-Hellman do provide high bit encryption, but to get back the original message with the increased level of encryption bits needs high computational powers as the device needs to find the factors that created the message after encryption which is much harder.
A basic idea on the functionality of ECC can help to understand the handshake and makes it easy for future troubleshooting.
An Elliptic Curve is a set of points which satisfies the below equation:
Below is how the curve would look like with values a = -1 and b = 1:
Figure: Elliptic Curve with values a = -1 and b = 1.
As seen from the curve, symmetry is noticed. Every non-vertical line passing through the curve intersects the same in 3 different points which is because of the elliptic nature of the curve. Another property of these curves is that the curve looks exactly the same below and above the x-axis. This is useful to plot different points on the curve which would be identical above and below x-axis. A straight line can be drawn after plotting the two points on the curve above and below x-axis. These properties help in achieving a better trapdoor function with less computational power.
Although it is very difficult to understand and explain ECC technology via blogs, a general idea of how the functions work helps. So to generalize the above, an ECC can be defined by picking any prime number as a maximum number, the equation as mentioned above with a and b values and a public point on the curve. Here, the private key is any number and the public key is dotted (point reflecting downwards from the orange point as shown from the graph for a non-vertical line — this is dotted once. Imagine dotting the same to the number of times equals to the private number) the number of times equal to the value of the private number. Based on the mathematics involved it becomes difficult to track the private key and hence helps in preventing offline dictionary attacks and achieve forward secrecy. Plus since the plot is already calculated and symmetric as mentioned earlier, the computational resources are not as high as RSA and Diffie Hellman based Cryptographic functions.
SAE Complete Handshake:
Please refer to the below Figure to understand WPA3 Communication along with SAE Handshake.
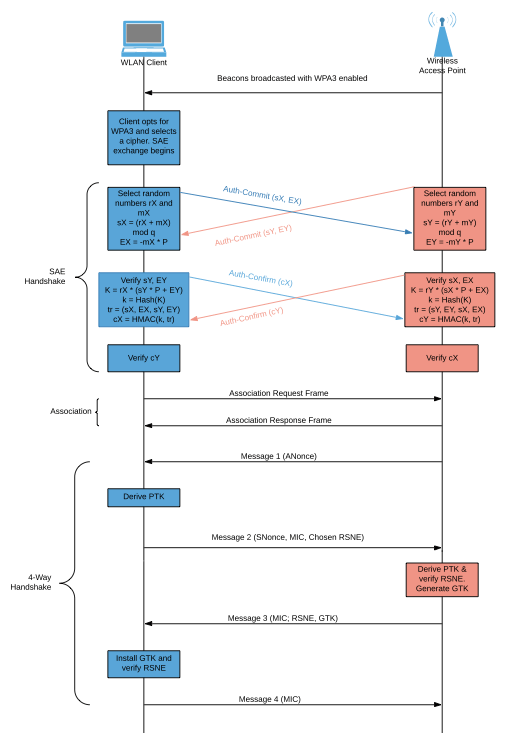
Figure: Complete WPA3 User and Client Communication along with SAE Handshake
Below are the steps the AP and the Client goes through in order to authenticate to a WPA3 based SSID:
- Access Points broadcasts beacons with WPA3 enabled. Alternatively, the SSID can be hidden and a Probe request can be sent by the user.
- The WPA3 capable client can see these beacons and with RSNE information in the beacons. It then selects a Cipher from the available options and starts the SAE Exchange.
- Note that the cross arrows indicate that the SAE exchange can happen concurrently i.e. the AP OR the WLAN client can initiate this exchange similar to a mesh connection. But since in normal WLAN infrastructure mode usually, the WLAN client initiates connection.
- The SAE Handshake starts after the client decides to connect to the SSID after selecting the suitable cipher.
- Below things should be noted before understanding SAE Handshake:
- a. All Elliptic Curves are defined over the equation y2=x3+ax+bmod p. Where p is a prime number and values a, b and p depend on the curve being used.
- b. For Elliptic Curve Groups modulo a prime (ECP) we will use G to determine the same and “q” to denote the prime order of G.
- c. When SAE is in progress, the user-readable password is converted into a group element using group mentioned in sub-step b. The resulting Password element is denoted by P.
- d. Random Number = ri which belongs to range [2, q]
- e. Random Mask = mi which belongs to range [2, q]
- f. The sum of points e and f = Ei = mi * P which belongs to the range [2, q]
- g. K is the shared secret Point
- h. Value k is the x-cordinate of the hash function of secret Point K
- i. Value tr is the handshake summary
- j. Value ci is calculated over HMAC of the Handshake summary is calculated using the key-value k.
- The SAE Exchange proceeds with two phases:
- a. Commit Phase: In this phase, Random numbers and masks calculation happens and the result scalar or integer is shared across. The Group Element Ei is then calculated and along with the Scalar si, the Ei is also sent as shown in the figure. On reception of these values, each party verifies the Scalar si if it belongs to the range between [1, q] and if the received group element Ei is a valid point on the curve being used. If any of these checks fails, the handshake is aborted. Forward secrecy can be achieved here based on the hardness of deriving mi given the Password Element P and Group element Ei used in the Elliptic curve discrete algorithm.
- b. Confirm Phase: In confirm phase, the Scalar and Group Elements values are verified as explained before. Then the shared secret point is calculated using the value K as shown in the figure. Finally the value ci is calculated as shown in sub-steps of step 5. If the ci values on both the ends are expected values, then the handshake succeeds and the key k becomes the PMK i.e Pairwise Master Key.
- The normal Association and 4-Way handshake follow using which PTK and GTK are generated.
Password Derivation:
It is interesting to understand how a password is derived from the commit phase of the SAE handshake. Also, the below steps would help to understand how the devices plot the password as an element in the elliptic curve:
- The pre-shared key OR Password is converted into a curve point using a hash-to-curve algorithm. This is done when generating the Commit Frame.
- This specific algorithm in SAE is based on trial and error. This means, it first hashes the password along with a counter (programmatic sequence) and the MAC address of both the stations. It then uses this output of the hash as x-coordinate on the curve.
- It then tries to find the solution for y using the equation y2=x3+ax+bmod p.
- If the solution exists, the points (x, y) becomes the Password Element P.
- If no solution is found, the counter is increased and another attempt is made.
- Finally to mitigate the timing attack the algorithm is run k times no matter when the solution for y is found. The extra iterations are calculated based on the random password generations rather than the original one.
- This is different from 802.11s where the iterations are limited to finding the solution for y. Although SAE was introduced in 802.11s amendment, an extended version of the same was introduced for 802.11.
WPA3 Transition Mode:
WPA3 by default uses MFP (Management Frame Protection – 802.11w) and is a mandatory requirement for both parties. It also helps for prevention against deauthentication attacks where an attacker tries to deauthenticate a legitimate client. Since not all devices in the WLAN architecture can support SAE of MFP, those devices cannot connect to a WPA3 based SSID. As mentioned earlier, WPA3 is backward compatible with WPA2. In WPA3 Transition mode, the MFP is set to optional. It also specifies that the AP supports both; 4-way handshake and SAE handshake without MFP. However, for a WPA3 connection, it is mandatory to use MFP.
So in all WPA3 does look promising with the added advantages with the usage of Elliptic Curve Cryptography to make WLAN more secure than ever before. However, there are still some hiccups in this approach that were overlooked. One of them is Dragonblood vulnerability which does open up some more discussions. However, more on that later!
2 thoughts on “WPA3 and DragonFly (SAE)”